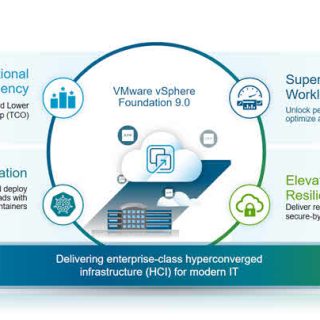
VMware vSAN is a powerful, software-defined storage solution that makes storage management easier by pooling local disks from ESXi hosts into a single storage platform. Its close integration with vSphere makes it a popular choice for organisations looking to modernise their infrastructure. However, implementing vSAN effectively necessitates a thorough understanding of its requirements and best practices.
This guide discusses VMware vSAN’s requirements, fault domain configurations, disk group design, host recommendations, and comparisons to block storage solutions such as Dell PowerStore and Unity. It also covers database deployment on vSAN and offers actionable tips to ensure a successful implementation.